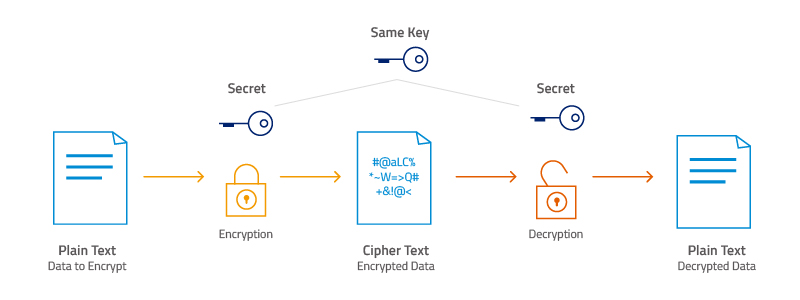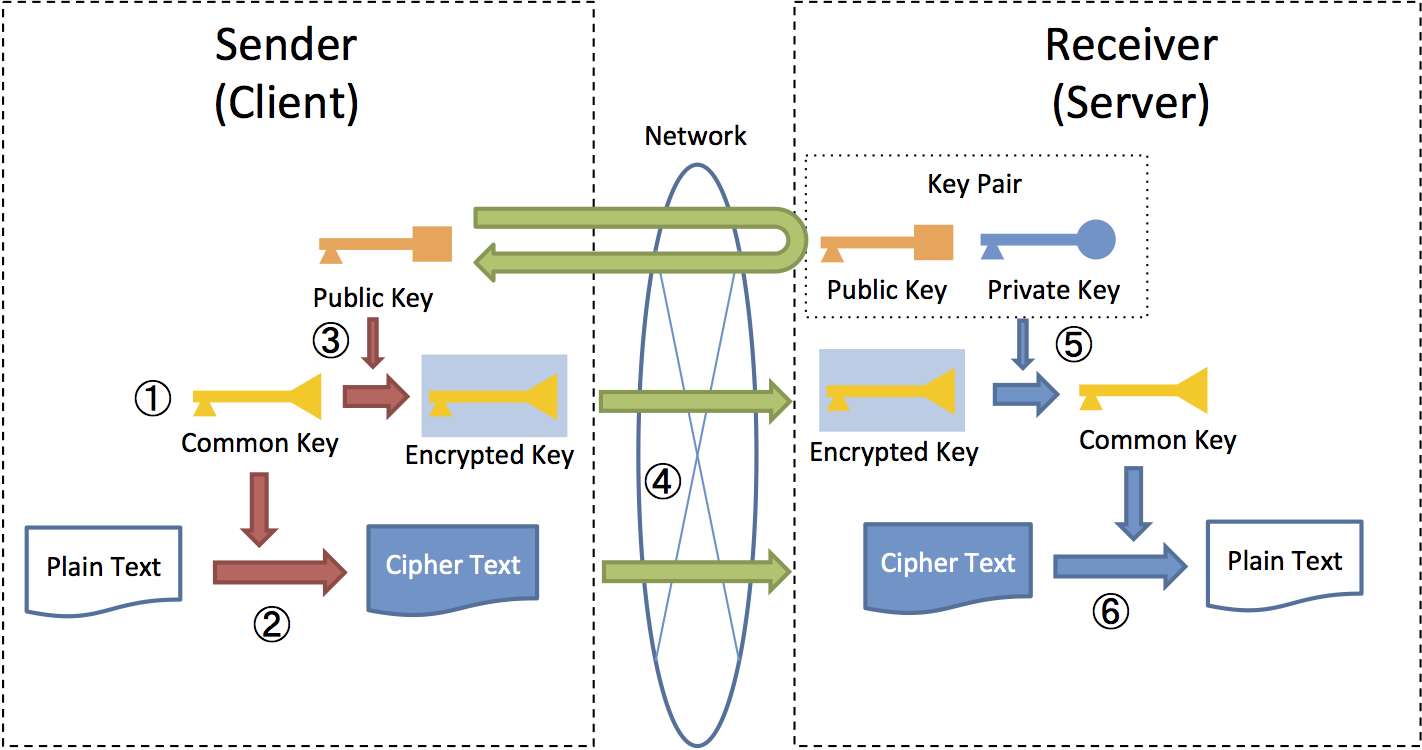
9.8. Encryption — TERASOLUNA Server Framework for Java (5.x) Development Guideline 5.3.1.RELEASE documentation
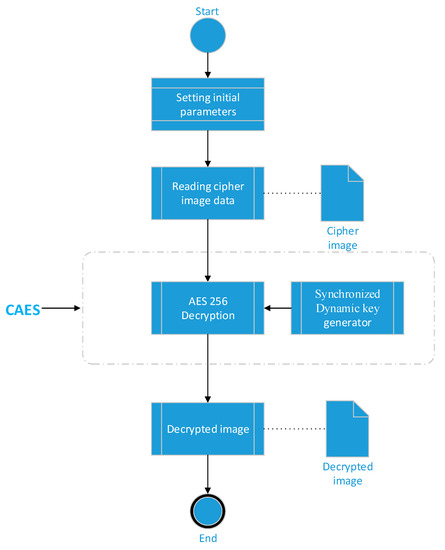
Applied Sciences | Free Full-Text | Chaos-Based Synchronized Dynamic Keys and Their Application to Image Encryption with an Improved AES Algorithm

Electronics | Free Full-Text | Magniber v2 Ransomware Decryption: Exploiting the Vulnerability of a Self-Developed Pseudo Random Number Generator

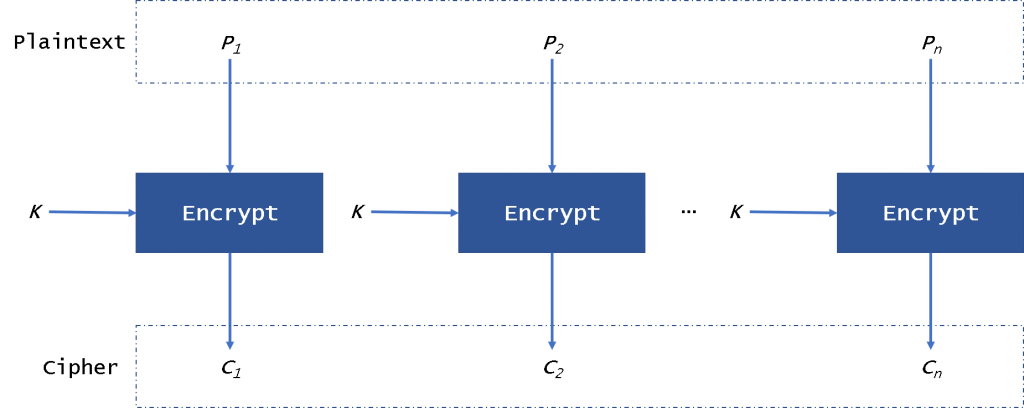
CBC (Cipher Block Chaining)-Based Authenticated Encryption for Securing Sensor Data in Smart Home | SpringerLink
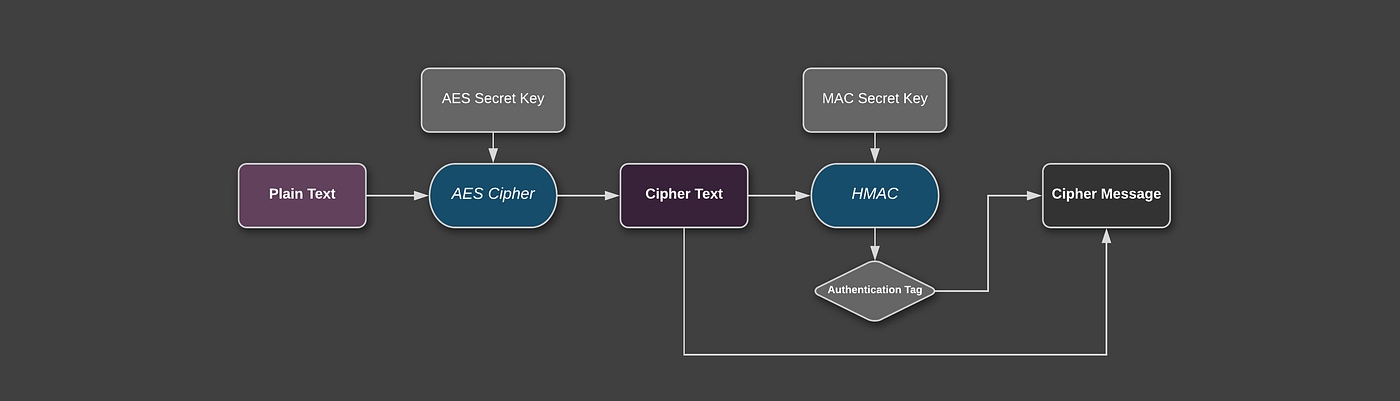
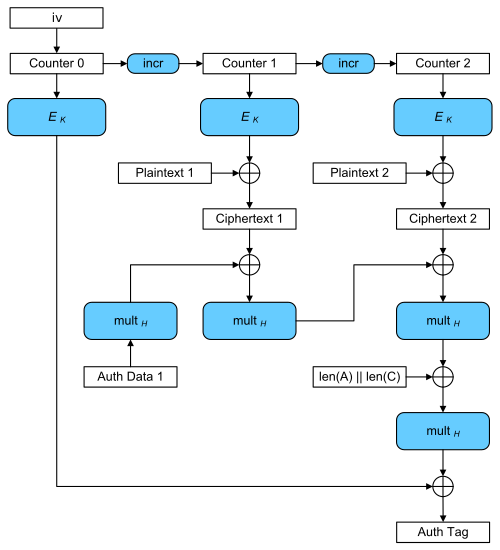
Security Best Practices: Symmetric Encryption with AES in Java and Android: Part 2: AES-CBC + HMAC | by Patrick Favre | ProAndroidDev