Photonics | Free Full-Text | Theoretical Demonstration of Security Improvement of Optical Phased Array Based on Optically Injection-Locked Lasers

The Art of Invisibility: The World's Most Famous Hacker Teaches You How to Be Safe in the Age of Big Brother and Big Data : Mitnick, Kevin: Amazon.de: Bücher
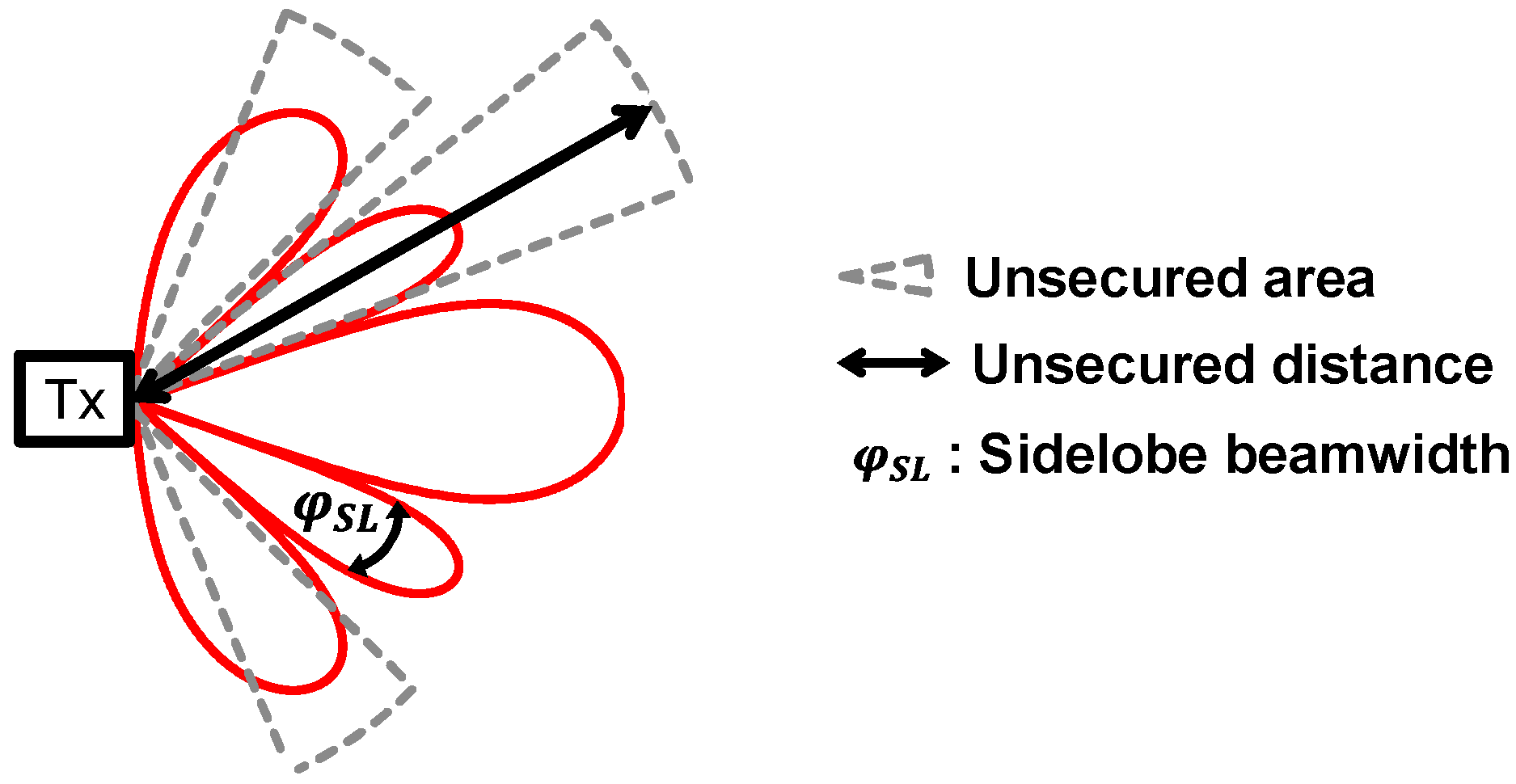
Photonics | Free Full-Text | Theoretical Demonstration of Security Improvement of Optical Phased Array Based on Optically Injection-Locked Lasers
Graphical illustration of the one way protocol with Gaussian channels.... | Download Scientific Diagram

Telehealth: It's Not about the Technology, It's about Expanding Access and Enhancing Treatment Services | PPT

The Art of Invisibility: The World's Most Famous Hacker Teaches You How to Be Safe in the Age of Big Brother and Big Data : Mitnick, Kevin: Amazon.de: Bücher







/cdn.vox-cdn.com/uploads/chorus_image/image/65647173/1076198768.jpg.0.jpg)

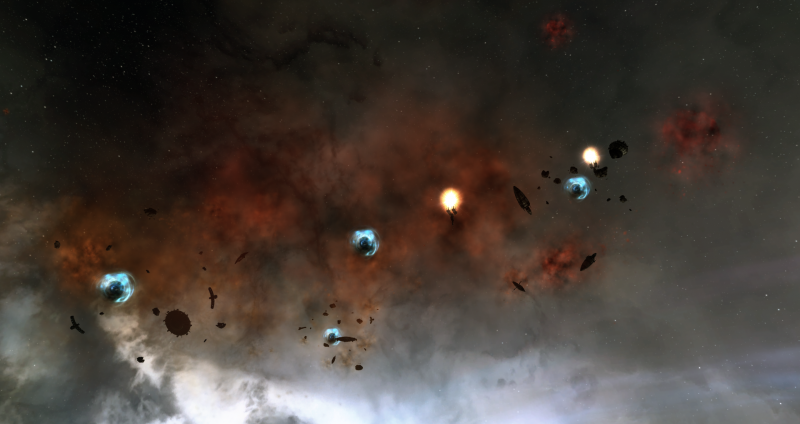
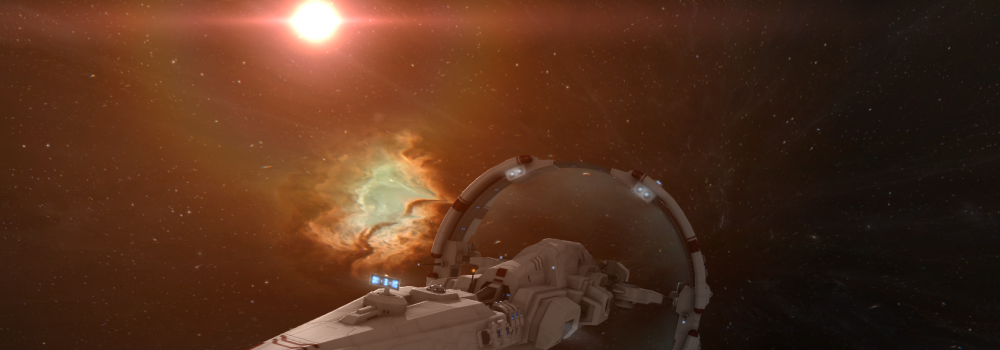
![[Video] Wolf-Rayet C13, every combat anomaly in Confessor : r/Eve [Video] Wolf-Rayet C13, every combat anomaly in Confessor : r/Eve](https://external-preview.redd.it/81y95LQXeW7XPkvk_oodUsfVjufMOQRzvdKApil-FH0.jpg?format=pjpg&auto=webp&s=bfd6ce7b2021964b3970c7b8a4c6cb237c6aa454)